Springtime is a great season in my household, as it normally indicates the start of the National Basketball Association (NBA) playoffs. Hope springs eternal for diehard basketball fans like yours truly as I either get to enjoy my favorite team attempt to grab the championship, or if you are a fan of the Phoenix Suns like I am over the last decade, you pick an alternative team because your hometown favorite until just recently has not made it to the postseason.
There are a number of individuals that can contribute to the makeup of the team that enable their performance. Ownership, team scouts, physical trainers and general managers can all contribute to the success of the team, but when it comes to game day, the one individual who sets up the game plan and makes the crucial calls during the game is the head coach. Deciding who is going to be on the floor and what plays are called lies with the primary decision maker: the head coach. I’ve been following basketball for a long time, and I don’t ever recall the head trainer or the general manager of a team coming out of the stands to draw up the game winning play at the end of the game.
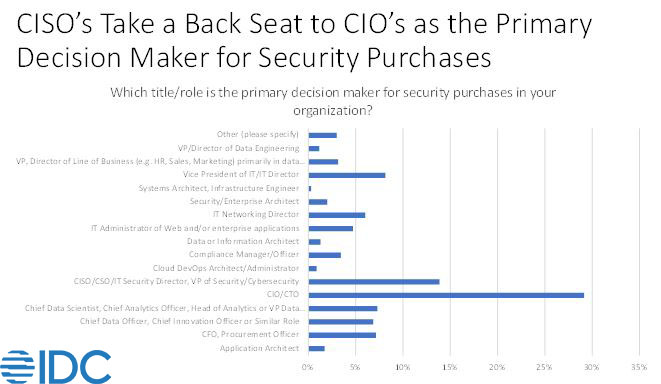
IDC recently published our Security ServicesView research that takes a look at various subjects and trends surrounding the who, what, why and how much questions that go into the purchasing of a myriad of security services. One of the questions that caught my attention was the continued dominance of the CIO/CTO role in being the primary decision maker for security purchases.
Granted, security has its roots in IT, and the best-case scenario would be a vision where IT, security, the rest of the C-Suite and the Board are sharing a common vision. Having a disjointed team that doesn’t fully understand the ramifications of their security purchases because the CISO is not fully engaged in the purchasing process is like having the head trainer setting starting lineups for a basketball team. It won’t be pretty.
What Does this Mean for Security Providers?
The struggle for CISOs to gain full control over their budget means that security providers need to diversify their sales approach. Yes, they still have the historical route to the organizational purse strings thru the CIO/CTO office, but they also need to be able to pitch their proposition to many different personas.
CFOs are enjoying the variable consumption model that the recent rush to the cloud that has allowed. In uncertain economic times, flexibility comes in 2nd only to cash on hand, and they will welcome proposals that allow them to consume security services that flex with economic conditions, just like they are able to do with their organizations cloud usage.
While still working to be the trusted voice to the CISO, security providers also need to expand their sales approach to other offices. The growth of personas like the Chief Compliance Officer and the Chief Risk Officer are increasing their collaboration with CISOs and can often have significant insights, of not final sign-off, on security initiatives.
The role of the Board can not be understated here as well. Their experience with dealing with multiple organizations means that they often have some experience, good or bad, with many different security providers. While they may not necessarily be the last check-off on a purchasing checklist, their experience and holistic views of the whole enterprise means that security providers need to be able to communicate their value proposition at the very highest levels of the organization.
What Do CISOs Need to Do to Gain Control Over Their Own Purchasing Decisions?
Ideally, the most qualified person should be the one with the final word on what vendors are utilized to provide the needed security platforms and services for the organization. To gain the trust needed to be the primary decision maker, CISOs need to continue to sharpen their business acumen, and be as comfortable being in a discussion around the supply chain logistics of their organization as they are discussing the open-source software utilized in their cloud apps.
Communication skills are another key attribute that may not necessarily be sought after as another certification to be added to the bottom of an e-mail signature, but it is a key skill that CISOs need to pick up. The tech community loves to speak in acronyms, and the cyber community is no different. Learning to speak in the jargon of the different personas that have an interest in the cost – and even more importantly – the capabilities of proposed security solutions is important.
What is the Ideal Persona to Make the Final Decision on Security Purchasing Decisions?
For too many years now, one of the common themes that comes out of the cyber security community has been the lack of qualified practitioners. STEM programs at colleges and universities have not been able to generate enough qualified people to fill the numerous vacant seats that need to be filled. More recently, organizations have seen the light and have expanded their potential candidate pool to include different skill sets.
Liberal Arts majors often have some of the soft skills that are needed to look at threat intelligence actors to model their tactics. Education majors can help with the internal training needs, or to help to set up some of the assessment exercises that are needed to prepare organizations for the next time that they need an incident response engagement. The point here is that just like the type of candidates that will fill seats in security operation centers is expanding, the pool of people that will at least have some say, if not the final say in security purchases, is expanding.
In an ideal world, the CISO should increasingly be the final voice that owns the decision on what their security architecture is going to look like. After all, if the high turnover that these security leaders is going to continue with forced departures still too often the norm, they should at least have the most say, if not the final say, for the security platforms and services that they are tasked with managing.
If CISOs are going to truly be the architect and the most trusted voice in the huddle of their internal security team, as well as the face of the security team to internal and external departments, they need to make sure that they are intimately involved in the major security purchasing decisions that they are tasked with utilizing. Playing good team ball by getting other departments to provide their input into these decisions, even when their input is not required, will help to give the CISO some gravitas in the organizations that they are tasked with protecting from ever increasing threats.
See more from IDC’s Security ServicesView to prioritize their security services investments, value proposition messages, delivery mechanisms, and partnerships in the market:




